- MS Exchange 2010 SP1 introduced, among other things, mailbox access audit feature that should help system administrators track users’ mailbox activity. While testing Exchange auditing capabilities I quite often bumped into some various issues and would like to present you with a series of articles about my mailbox access audit tests and their results. We can walk together through the steps of setting up a mailbox access auditing for the particular actions and compare the test results with the expected ones.
- From my point of view one of the most important user actions an administrator should be able to audit is Delegate mailbox access. For instance, if I give User1 Full Access permission to User2’s mailbox I’d like to know what actions (and when) will be accomplished by User1 in the Users2’s mailbox. In this article I want to focus on some practical approaches to mailbox access audit for delegate users.
- The first question I want answered is “who and when accessed a delegated mailbox”.
- Consider this situation: User1 needs access to User2’s mailbox. Let’s walk through the steps necessary for granting the requested access and monitoring its usage.
1) In Exchange Management Console we give User1 Full Access permission to User2’s mailbox:
- 2) …then turn on mailbox access audit for User2’s mailbox:
- Set-Mailbox -Identity User2 -AuditEnabled $true

4) Pay close attention to what actions are audited by default: as we’re going to use the delegate access Update, SoftDelete, HardDelete, SendAs and Create actions will be audited by default once mailbox access is enabled for a particular mailbox. So to be able to audit the access to User2’s mailbox we must add FolderBind action to the list of already audited actions
- Set-Mailbox -Identity User2 -AuditDelegate Update,SoftDelete,HardDelete,SendAs,Create,FolderBind -AuditEnabled $true
- and check they have been applied correctly:
- Get-Mailbox User2 |FL *audit*

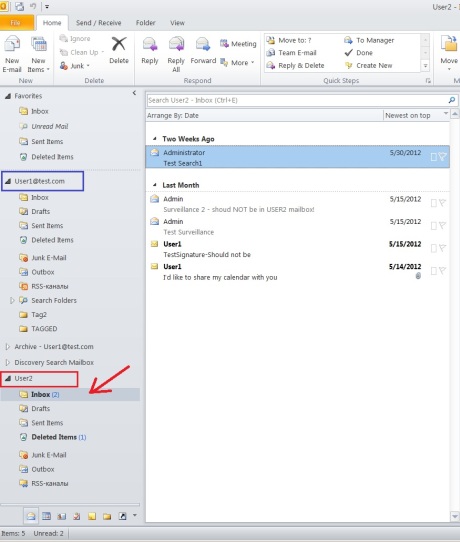
5) Now let’s start Outlook and log on to User1’s mailbox. Outlook will open the additional User2’s mailbox for User1 automatically:
- 5) Now let’s check if any log records was generated when Outlook was started:
- Search-MailboxAuditLog -Identity User2 -LogonTypes Delegate -StartDate 6/14/2012 -EndDate 6/15/2012 -ResultSize 2000

Yes, here we can see a brief description of the fact that someone accessed User2′s mailbox. As our goal is to get all availabale information about Delegate access to User2′s mailbox we should add -ShowDetails to the previuos command:
6) Search-MailboxAuditLog -Identity User2 -LogonTypes Delegate -StartDate 6/14/2012 -EndDate 6/15/2012 -ResultSize 2000 -ShowDetails
What is it? Search-MailboxAuditLog cmdlet stops producing any output should I add -ShowDetails switch!
The output expected should contain the following fields: Operation, OperationResult, LogonType, …, ClientIPAddress and many others as described here: http://technet.microsoft.com/en-us/library/ff459237.aspx
I know for sure that at least in some cases Search-MailboxAuditLog cmdlet with the swith -ShowDetails works correctly but I can’t explain what it does not work in this particular test.
However, let’s try to use the other tool for reading mailbox access audit log – the Exchange Control Panel.
- Log in to ECP under account that is a member of Exchange Organization Management group or Records Management group (for instance, Administrator account) and click “Run a non-owner mailbox access report”
Here it is! This report contains a bit more information about the FolderBind action, at least we can see which user (User1) opened User2′s mailbox.
- Look! There are multiple occurrences of Delegate Access actions at 6:08Am. This is because FolderBind actions performed by delegates are consolidated. One log entry is generated for individual folder access within a time span of three hours.
-
Summary
- This was the first test for Exchange Server 2010 SP1 mailbox auditing. In the next article we’ll continue to work with the mailbox Delegate Access.
- The new article on the Exchange Server 2013 describing the same test is now available here: https://michaelfirsov.wordpress.com/exchange-2013-mailbox-auditing-part-i/